Hi Terry, Sorry I was not clear enough in my suggestion and putting it into context… we’re on the same page, there are currently discussions going on in some communities to extend TLP scheme (proprietary) by validation information and within some schemes used in intel (usually not public / publicly known) this is already existing as part of their schemes. Unfortunately proprietary approaches have their issues when trying to make it work outside the origin.
To enable a true policy-based management, enforcement, priority handling etc. it’s vital to have a standard on assigning & processing level of confidence, trust in source and possibly validation by analyst as well. Some of the European ISACs I know handle this by reserving some classification levels for members and assign trust-by-default but of course this does not scale beyond limited community nor is it a feasible way to apply it on granular objects.
Cheers from Brussels,
Joerg
From: cti@lists.oasis-open.org [mailto:cti@lists.oasis-open.org]On Behalf Of Terry MacDonald
Sent: Wednesday, September 7, 2016 21:11
To: JE <je@cybersecurityscout.eu>
Cc: cti-stix@lists.oasis-open.org;cti@lists.oasis-open.org; Thompson, Dean <Dean.Thompson@anz.com>
Subject: RE: [cti] CTI Brussels F2F Meeting...RSVP deadline 5 September
Hi Joerg,
I wasn't meaning information handling or policy management at all, as this is already supported via the object level data marking or granular date marking in STIX 2.0.
I was definitely meaning a way of describing confidence that the threat intelligence is correct, and confidence that the person who told you the threat intelligence gets it right. We had that functionality in STIX 1.x series, and we've lost it in STIX 2.0.
We need to add it back on as part of STIX 2.1.
Cheers
Terry MacDonald
Cosive
On 7/09/2016 10:25 PM, "JE" <je@cybersecurityscout.eu> wrote:
Dear All,
I fully support this – having built some ISACs in industry as well as GOV classification/labeling is usually a “top 5 “ issue … if not at the time of initial set-up than usually later when information from different sources is to be shared and utilized. This might not be a primary issue from vendor side (although it should be as most TI is not under monolithic policy/license rights but compiled) it is definitely an issue from user perspective to handle, distribute and leverage TI properly,
Some of the commercially available systems on the market implement labeling/label-based-handling in a proprietary way as current information models/standards do not foresee this. If you e.g. look at OTRS (not a STIX/TAXI implementation but wide used for Service + Incident Mgt), actually an open source system but during the evolution also included labeling and handling according to this. No matter if e.g. TLP or other schemes are applied I strongly suggest to at least include the option to label objects and though enable/apply/enforce policy-based information exchange and handling.
Sunny greetings from Berlin & looking forward meeting you guys f2f on later Wednesday evening in Brussels,
Joerg
From: cti@lists.oasis-open.org [mailto:cti@lists.oasis-open.org]On Behalf Of Thompson, Dean
Sent: Wednesday, September 7, 2016 03:06
To: 'Terry MacDonald' <terry.macdonald@cosive.com>; 'cti@lists.oasis-open.org' <cti@lists.oasis-open.org>; 'cti-stix@lists.oasis-open.org' <cti-stix@lists.oasis-open.org>
Subject: RE: [cti] CTI Brussels F2F Meeting...RSVP deadline 5 September
Hi!,
Can I add my voice in here as well and say that “Confidence” and also having an “Opinion” about Threat Intelligence is very important and is a concept that we use quite heavily when we are exchanging threat intelligence with other financial organisations and dealing with threat data that comes in via 3rd parties and intelligence sources.
Can we please ensure that this is included in the agenda and discussed at the meeting ?
Regards,
Dean
From: cti@lists.oasis-open.org [mailto:cti@lists.oasis-open.org]On Behalf Of Terry MacDonald
Sent: Wednesday, 7 September 2016 8:18 AM
To: cti@lists.oasis-open.org;cti-stix@lists.oasis-open.org
Subject: Re: [cti] CTI Brussels F2F Meeting...RSVP deadline 5 September
Please say that we are including confidence and opinion object in STIX 2.1 candidate smackdown agenda item at the F2F.
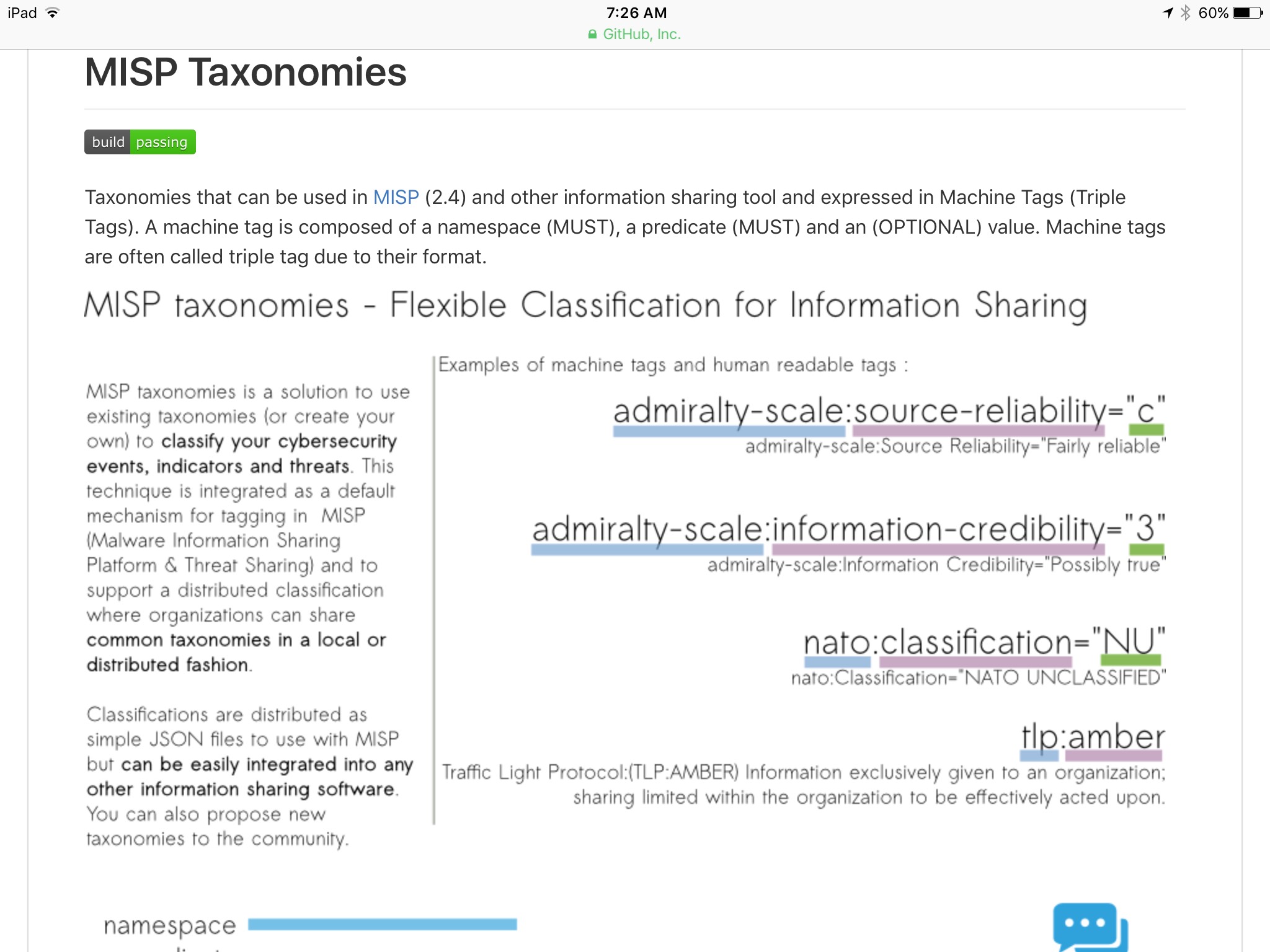
We just can't treat everything that people send out as the absolute truth as we do in STIX 2.0. There is a reason things like the admiralty code were developed.... and that's because threat intelligence is always someone's opinion.We need a way for the consumer to understand how confident the producer is in the threat intelligence they are sending. It's up to the consumer to determine if they believe that its the truth, and they need various ways to determine this. That's a ton easier if the person who sent the threat intelligence to you tells you how much they trust the intelligence and trust the source of the intelligence with some form of confidence field.....
I really, really believe this is critical for STIX to work properly, and it was something that made it possible for STIX to automatically be pushed out to the different security tools within an organization (e.g. high confidence DNS to the DNS RPZ block, low confidence to the alerting on the passive DNS).
These are so easy to add to STIX, we would be remiss to skip it.
Cheers
Terry MacDonald| Chief Product Officer

M: +64 211 918 814
E: terry.macdonald@cosive.com
W: www.cosive.com
On Fri, Sep 2, 2016 at 8:53 AM, Jane Harnad <jharnad@oasis-open.org> wrote:
Dear CTI Members,
The CTI TC F2F meeting is scheduled for Wednesday, 7 September at the Thon EU Hotel, Germany Room. Lunch and refreshments will be provided by OASIS. A headcount is needed ASAP. Below is a list of individuals that replied to the last RSVP request. If you don't see your name and do plan to participate in either the F2F meeting or group dinner, please send your RSVP no later than 5 September.
Remote access is available to TC members unable to attend in person.
Login details are:
https://global.gotomeeting.com/join/978573765
You can also dial in using your phone.
United States (Toll-free): 1 866 899 4679
United States +1 (646) 749-3117
Access Code: 978-573-765
Proposed agenda is attached.
Details on group dinner option: CTI members are invited to sign up to attend a group dinner on Wednesday evening after the F2F. Family members and/or guests traveling along with you are also invited to join us. This is not a hosted dinner, so each participant (and their guests) will be responsible for covering the costs associated with their dinner. Please be sure to confirm the number of guests.
Thanks so much and we look forward to seeing you all in Brussels!
Regards, Jane
**F2F/Dinner Attendees